Cyber Security Alerts
- Home
- Cyber Warfare Defense Toolkit
- Cyber Security Alerts
The Latest Cyber Security News and Information
Stay up-to-date with the latest news, scam reports and tips to help mitigate your risk of a cyber attack.
Pandemic Unemployment Assistance - Fraud Alert
April 13, 2021
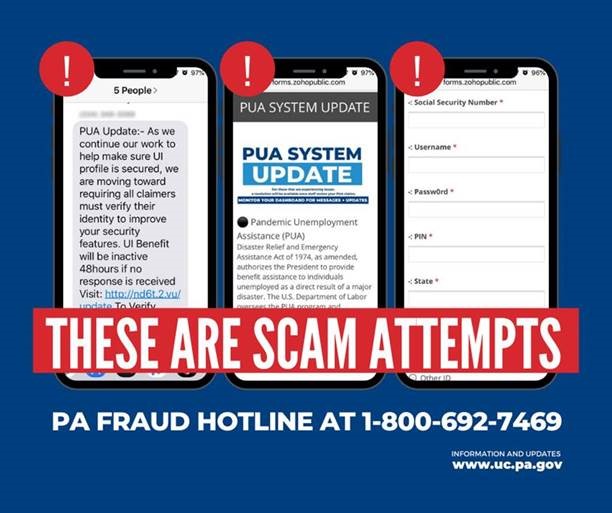
The Pennsylvania Department of Labor & Industry’s security vendor has identified additional phishing attempts and fraud scams leveraging social media, text messaging, and email to lure unsuspecting individuals into providing personal information so that the scammers can claim their identity for Pandemic Unemployment Assistance (PUA).
The most recent scams include but are not limited to telling individuals they’ve won contests, won a cash prize, being eligible for a monetary award for applying for benefits, or offering an alternative or “faster” application or mobile app to apply for regular unemployment or PUA benefits.
- ATTN: Scammers are asking PUA claimants to verify their identity via text messages/web forms -- THIS IS A SCAM! (see below for example)
- The only way to verify identity is via ID.ME and NEVER via text messages or web forms.
- If you see this, please report or visit www.uc.pa.gov and select the “REPORT FRAUD” icon.
Below are actual messages related to PUA sent to individual cell phones:
CRITICAL Update
March 2nd, 2021
Microsoft has detected multiple 0-day exploits being used to attack on-premises versions of Microsoft Exchange Server in limited and targeted attacks. In the attacks observed, the threat actor used these vulnerabilities to access on-premises Exchange servers which enabled access to email accounts and allowed installation of additional malware to facilitate long-term access to victim environments. Microsoft Threat Intelligence Center (MSTIC) attributes this campaign with high confidence to HAFNIUM, a group assessed to be state-sponsored and operating out of China, based on observed victimology, tactics and procedures. – Microsoft
On March 3rd, the Cybersecurity Infrastructure Security Agency (CISA), issued Emergency Directive (ED) 21-02 and Alert AA21-062A addressing critical vulnerabilities in Microsoft Exchange products. - CISA
Please apply the following Microsoft patches ASAP:
CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, CVE-2021-27065
COVID-19 phishing lures still working for cyber adversaries.
January 2021
COVID-19-themed cyberattacks are ongoing and now focused on big corporations, governments, and critical infrastructure. According to a recent report, the COVID-19 pandemic was a core element in phishing campaigns in 2020. Besides hacking attacks, recent incidents also involve manipulation of stolen documents in an attempt to raise doubts about the vaccine and the work of the European Medicines Agency (EMA). In the last two months, the major sectors affected by Coronavirus-themed attacks are healthcare, government, and financial services. North America, South-east Asia, and Europe were amongst the most affected regions. Scammers were found to be using social engineering emails and messaging apps to lure victims with fake claims that they can deliver COVID-19 shots within days for a price tag of $150. Last month, Pitkin County in the U.S. state of Colorado became aware of potential unauthorized access to a file including information regarding COVID-19 case investigations and contact tracing. Cybercriminals are likely to continue their Coronavirus-themed attacks taking advantage of public concern regarding the pandemic. Therefore, experts suggest organizations encrypt sensitive data, segregate networks, provide training to identify phishing emails, and stay alert while surfing online. - Cyware
Text messages promising $1,200 stimulus checks are scams, IRS warns.
December 2020
The IRS and a coalition of state tax agencies and tax industry officials are warning individuals who receive text messages promising that money is trying to lure unsuspecting individuals into providing their financial details. The text scam typically reads, “You have received a direct deposit of $1,200 from COVID-19 TREAS FUND. Further action is required to accept this payment into your account. Continue here to accept this payment…” The IRS is reminding people that it does not send these kinds of unsolicited texts or emails, never demands tax payments via gift cards nor does it threaten people with jail or lawsuits. (CNBC)
Protecting Older Adults from Contact Tracing Scams
November 2020
As COVID-19 remains a threat in the commonwealth, the Department of Aging is joining the Department of Health to warn everyone, especially older adults, about contact tracing scams. Contact tracing is the process of identifying people who came into contact with someone who has tested positive for COVID-19 so that they can quarantine and monitor for symptoms. Scammers are attempting to take advantage of how this process works by pretending to be contact tracers and trying to get personal information out of victims through phone calls or electronic messages.
A contact tracer may ask:
- For verification of someone’s date of birth, address, and any other phone numbers they may have; and
- If someone has already tested positive for COVID-19, they may also ask for the date and location of where that person was tested.
A contact tracer will never ask for:
- Social Security Numbers, financial or bank account information, or personal details unrelated to a person’s potential exposure to someone with COVID-19;
- Personal information through SMS/text message or send someone to any website link asking for personal information;
- Photographs or videos of any kind;
- Passwords; or
- Money or payment.
A contact tracer will never share a person’s information with any local, state or federal law enforcement agency. For more information about the contact tracing process, visit the Department of Health’s website.
- Pennsylvania Department of Banking and Securities
Cyber Actor Spoofing COVID-19 Loan Relief Webpage via Phishing Emails
August, 2020
The Cybersecurity and Infrastructure Security Agency issued an alert today regarding an unknown malicious cyber actor targeting small business owners through phishing emails containing links that redirect victims to a spoofed Small Business Administration COVID-19 relief webpage used to steal credentials.
The phishing email contains:
- A subject line, SBA Application – Review and Proceed
- A sender, marked as disastercustomerservice@sba[.]gov
- Text in the email body urging the recipient to click on a hyperlink to address:
- hxxps://leanproconsulting[.]com.br/gov/covid19relief/sba.gov
If you see one of these emails, delete it.
- CISA
SBA Programs - Scams and Fraud Alerts
July, 2020
Beware of Scams and Fraud Schemes
The Office of Inspector General recognizes that we are facing unprecedented times and is alerting the public about potential fraud schemes related to economic stimulus programs offered by the U.S. Small Business Administration in response to the Novel Coronavirus Pandemic (COVID-19). The Coronavirus Aid, Relief, and Economic Security Act (CARES Act), the largest financial assistance bill to date, includes provisions to help small businesses. Fraudsters have already begun targeting small business owners during these economically difficult times. Be on the lookout for grant fraud, loan fraud, and phishing.
Grants: SBA does not initiate contact on either 7a or Disaster loans or grants. If you are proactively contacted by someone claiming to be from the SBA, suspect fraud.
Loans: If you are contacted by someone promising to get the approval of an SBA loan, but requires any payment upfront or offers a high-interest bridge loan in the interim, suspect fraud.
Phishing: If you are in the process of applying for an SBA loan and receive email correspondence asking for PII, ensure that the referenced application number is consistent with the actual application number. Look out for phishing attacks/scams utilizing the SBA logo. These may be attempts to obtain your personally identifiable information (PII), to obtain personal banking access, or to install ransomware/malware on your computer.
Report Fraud:
Report any suspected fraud to OIG’s Hotline at 800-767-0385 or online at, https://www.sba.gov/about-sba/oversight-advocacy/office-inspector-general/office-inspector-general-hotline.
- Small Business Administration: https://www.sba.gov/document/report-sba-programs-scams-fraud-alerts
Coronavirus scams and malicious attacks
February 19, 2020
“Scammers are taking advantage of fears surrounding the Coronavirus," the FTC says. "They’re setting up websites to sell bogus products, and using fake emails, texts, and social media posts as a ruse to take your money and get your personal information. "The emails and posts may be promoting awareness and prevention tips, and fake information about cases in your neighborhood. "They also may be asking you to donate to victims, offering advice on unproven treatments, or contain malicious email attachments."
The FTC also provides the following measures you can take to make sure that you won't get scammed or get your computer infected with malware after falling for a scammer's tricks:
- Don’t click on links from sources you don’t know. It could download a virus onto your computer or device. Make sure the anti-malware and anti-virus software on your computer is up to date.
- Watch for emails claiming to be from the Centers for Disease Control and Prevention (CDC) or experts saying that they have information about the virus. For the most up-to-date information about the Coronavirus, visit the Centers for Disease Control and Prevention (CDC) and the World Health Organization (WHO).
- Ignore online offers for vaccinations. If you see ads touting prevention, treatment, or cure claims for the Coronavirus, ask yourself: if there’s been a medical breakthrough, would you be hearing about it for the first time through an ad or sales pitch?
- Do your homework when it comes to donations, whether through charities or crowdfunding sites. Don’t let anyone rush you into making a donation. If someone wants donations in cash, by gift card, or by wiring money, don’t do it.
- Be alert to “investment opportunities.” The U.S. Securities and Exchange Commission (SEC) is warning people about online promotions, including on social media, claiming that the products or services of publicly-traded companies can prevent, detect, or cure Coronavirus and that the stock of these companies will dramatically increase in value as a result.
-CDC & FTC
How to Avoid Small Business Scams.
November 5, 2019
There was a 424% increase in new small business cyber breaches last year. – 4iQ
- If you’re not expecting an email, and it looks suspicious email, delete it.
- Do not click links to unknown websites, and if you are asked to enter your details, including passwords and credit card details, for unverified reasons, leave the site immediately.
- Verify the company’s and supplier’s you plan on working with, check to see how long they have been in business, perform due diligence, and talk to one of their existing customers.
- Carefully check all the invoices you get, the items listed, and the business or supplier name before handing any payment. Billing schemes are ranked as the second most common fraud at 29% for organizations with fewer than 100 employees.
- Be careful about the information you give out about your business. Make sure that the person or organization you are giving it to is trustworthy and that you know what your business details will be used for.
- Limit the number of people that are authorized to order, receive invoices, and make payments for your business.
Google Confirms Serious Chrome Security Problem - Here's How To Fix It
September 17, 2019
“Google Chrome's security lead and engineering director, Justin Schuh, has warned that users of the most popular web browser should update "like right this minute." Why the urgency? Simply put, there is a zero-day vulnerability for Chrome that the Google Threat Analysis Group has determined is being actively exploited in the wild. What does that all mean? Well, a vulnerability is just a bug or flaw in the code and while they all need to be fixed, not all of them either can be or are being exploited. A zero-day vulnerability is one that threat actors have managed to create an exploit for, a way of doing bad things to your device or data before the good guys even knew the vulnerability existed. In other words, they have zero days in which to issue a fix. The bad news for users of Google Chrome is that this particular zero-day vulnerability, CVE-2019-5786, is already being exploited by the bad guys. Which is why it's so important to make sure your browser has been updated to the latest patched version that fixes the vulnerability.” - Forbes
How this can be fixed:
Luckily this is an easy problem to fix, just make sure you do it as soon as you've finished reading this! First, head over to the drop-down menu in Chrome (you'll find it at the far right of the toolbar - click on the three stacked dots) and select Help|About Google Chrome. You could also type chrome://settings/help in the address bar if you prefer, which takes you to the same dialog box. This will tell you if you have the current version running or if there is an update available. To be safe from this zero-day exploit, make sure that it says you are running version 72.0.3626.121 (Official Build). If not, then Chrome should go and fetch the latest version and update your browser for you automatically.
Previous Alert
September 1, 2019
“Google Chrome's security lead and engineering director, Justin Schuh, has warned that users of the most popular web browser should update "like right this minute." Why the urgency? Simply put, there is a zero-day vulnerability for Chrome that the Google Threat Analysis Group has determined is being actively exploited in the wild. What does that all mean? Well, a vulnerability is just a bug or flaw in the code and while they all need to be fixed, not all of them either can be or are being exploited. A zero-day vulnerability is one that threat actors have managed to create an exploit for, a way of doing bad things to your device or data before the good guys even knew the vulnerability existed. In other words, they have zero days in which to issue a fix. The bad news for users of Google Chrome is that this particular zero-day vulnerability, CVE-2019-5786, is already being exploited by the bad guys. Which is why it's so important to make sure your browser has been updated to the latest patched version that fixes the vulnerability.”


